David Spring M. Ed. December 2, 2013
Notes: The original version of this article was published on my old website Free Yourself From Microsoft and the NSA dot org on December 2 2013. Nearly one million people read this article as it was shared by groups around the world. It caused such a firestorm that I spent a huge amount of time answering emails about the article. I therefore took the article down a few years later. However, an edited version of this article was also posted on a website called Oped News dot com on December 5, 2013. It is still there at this link: http://www.opednews.com/articles/Connecting-the-Dots-betwee-by-David-Spring-Spying-131206-522.html
Here is the unedited version of the article: In the past three months since I published Free Yourself from Microsoft and the NSA, there has been a steady stream of increasingly shocking revelations about the extent of NSA spying in the US and around the world. NSA operatives have been caught spying on their wives and girlfriends. The NSA has also been caught spying on dozens of world leaders including Angela Merkel, the elected leader of Germany and the Pope in the Vatican, the leader of the Catholic Church. http://news.panorama.it/cronaca/papa-francesco-datagate

Clearly Angela Merkel and the Pope are not “terrorist threats.” In fact, the greatest threat to democracies around the world is the out of control lunatics pulling the strings at the NSA.
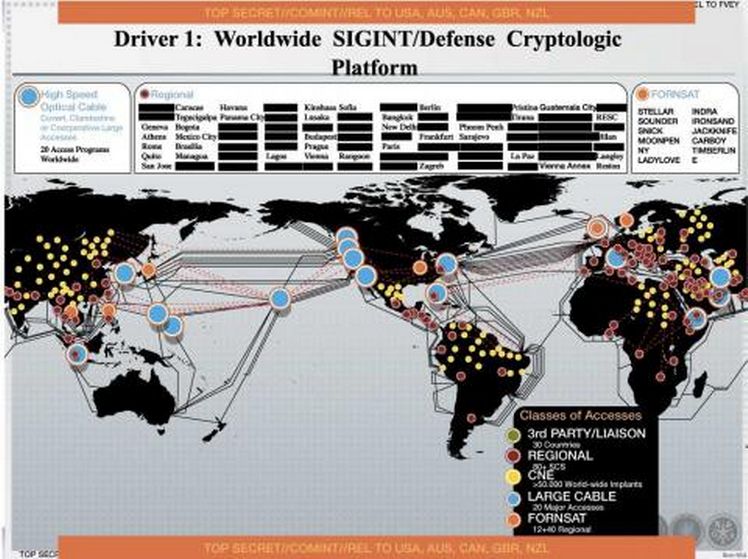
At the recent trial of hacker Jeremy Hammond, it was revealed that the NSA and FBI paid an informant named Sabu to help Jeremy Hammond hack into various government websites and computer systems all around the world. In November 2013, it was revealed that the NSA has hacked into more than 85,000 Windows computer networks around the world.
https://portside.org/2013-11-24/nsa-infected-50000-computer-networks-malicious-software
https://techcrunch.com/2013/11/23/nsa-has-50000-digital-sleeper-agents-snowden/
This article provides evidence of several shocking links between Microsoft, the NSA and Bitcoin indicating a diabolical plot to manipulate, undermine and corrupt the development of alternative digital currencies.
As financial analyst, Greg Mannarino recently said, “We already have a digital currency. It is called the US dollar.” It appears that the NSA wants to insure that no credible alternative to the US digital dollar arises. They therefore created and sabotaged Bitcoin in order to undermine digital currencies.
I realize what I am about to describe may seem difficult to believe. But these are only the latest of many examples of Microsoft and the NSA doing things that are very evil in order to gain control over the entire planet. In fact, the NSA makes the Mafia look like a gathering of Sunday school teachers. The NSA’s goal, from a February 2012 document, as confirmed by Snowden releases on November 22, 2013, is to extract all data on “anyone, anytime, anywhere” by influencing (corrupting) the “global encryption market.” This goal is evidence of the NSA’s evil intentions.
http://www.nytimes.com/2013/11/23/us/politics/nsa-report-outlined-goals-for-more-power.html?_r=0
The full extent of the NSA’s diabolical plot was first brought to light on September 5, 2013 when Glenn Greenwald (and several others) exposed a new batch of top secret NSA documents with articles in the Guardian, the New York Times and ProPublica. The following three articles describe a $4 billion16 year NSA bribery and kickback scheme called Bullrun which has severely corrupted encryption standards used to secure financial and other sensitive records.
http://www.theguardian.com/world/2013/sep/05/nsa-gchq-encryption-codes-security
http://www.nytimes.com/2013/09/06/us/nsa-foils-much-internet-encryption.html?_r=0
http://www.propublica.org/article/the-nsas-secret-campaign-to-crack-undermine-internet-encryption
The Bullrun program is much bigger and much more dangerous than the NSA PRISM program exposed in June 2013. The following is from the actual 2010 NSA memos which describe Bullrun:
“For the past decade, NSA has led an aggressive, multipronged effort to break widely used Internet encryption technologies.” This NSA plot “actively engages the U.S. and foreign IT industries to covertly influence and/or overtly leverage their commercial products’ designs” to make them “exploitable.”
In other words, the NSA bribes companies like Microsoft with hundreds of millions of dollars every year in order to insert flaws into their computer programs.
As noted earlier, in November 2013, it was revealed that the NSA has hacked into more than 85,000 Windows computer networks around the world. This raises the question of how the NSA is gaining access to these computer networks. One method is the backdoor key Microsoft gave the NSA in 1998, as I describe in detail in my book. However, the Bullrun program means that the NSA is also using deliberately flawed encryption programs to gain access to computer networks. The NSA refers specifically to using encryption keys in their 2013 budget request as being needed to “influence policies, standards and specifications for commercial public key technologies.”
Public key technologies are the most commonly use of encryption methods. A public key is like a password. For example, if the password to your bank account is TakeMyMoney, the encrypted version of your password might be XQ4%zv20#49. A public/private key combination is used to translate the password back into TakeMyMoney. At the heart of all “key” programs are random number generators that make it hard for hackers to translate the encrypted password unless they possess the all-important keys.
Encryption is the Achilles heel of internet and computer security. Without encryption there is no security.
It is therefore essential to understand the history of how NSA corrupted crucial NIST (National Institute of Standards and Technology) encryption standards if we have any hope of getting back to internet security. Thanks to Snowden, we now know that in early 2006, the NSA insisted on adding an unsafe “elliptic curve based random number generator” created by the NSA to three other more secure encryption methods that had already been researched and approved before the NSA take over. The corrupted standard is in NIST Special Publication 800-90. For more details, see
http://www.propublica.org/article/standards-agency-strongly-suggests-dropping-its-own-encryption-standard
On May 29, 2006, a pair of researchers in the Netherlands authored a paper showing that this NSA created elliptic curve based random number generator was insecure and that attacks against it could “be run on an ordinary PC.”
http://s3.documentcloud.org/documents/786216/cryptanalysis-of-the-dual-elliptic-curve.pdf
The math used by the Netherlands researchers was rather complex. A less complex explanation of the danger of this bad NSA encryption method was presented in August 2007 by two junior Microsoft employees at an internet security conference in Santa Barbara California. .
http://www.wired.com/images_blogs/threatlevel/2013/09/15-shumow.pdf
This presentation occurred at almost the exact same time that Microsoft joined the NSA’s PRISM program and made dangerous modifications to the UEFI computer startup program (described in detail in my book). While there are many families of elliptical functions, all of them suffer from the same problem described by these researchers. Basically, elliptical curves are either too complex to be used for encryption without certain restrictions (such as limiting the elliptical curve function to integers) - or they are not random if there are restrictions.
The NSA must have had a purpose in mind in putting such a bad encryption method into the national standard list of approved encryptions. I therefore started researching applications that used this bad NSA encryption method.
One application was the Windows operating system. Despite the fact that it was known to be insecure, Microsoft added this NSA fake encryption method to Windows Vista in February 2008. Even though the NSA flawed process was not the default encryption method, adding it to the Windows operating system made it much easier for the NSA to attack Iranian Windows computer systems later that same year. The NSA also likely used this same method to attack over 50,000 other Windows computer networks around the world in the next two years. The number is now over 85,000 compromised computer networks per a leak of top secret NSA documents released on November 23, 2013.
“The malware can be controlled remotely and be turned on and off at will. The ‘implants’ act as digital ‘sleeper cells’ that can be activated with a single push of a button. According to the Washington Post, the NSA has been carrying out this type of cyber operation since 1998.”
http://www.nrc.nl/nieuws/2013/11/23/nsa-infected-50000-computer-networks-with-malicious-software/
Among the other applications that adopted the flawed NSA encryption scam was Bitcoin, the world’s largest and most successful digital currency program.
In fact, several lines of evidence indicate that Bitcoin was developed by the NSA between 2006 and 2008 – around the same time that the NSA sabotaged the NIST encryption standards. The domain name registration for Bitcoin was in August 2008 and the first paper was published in November 2008. The production of the first bitcoins was in January 2009. The NSA elliptical encryption method was and still is used to verify the authenticity of bitcoin ownership as one of the final steps in transferring ownership of bitcoins.
This is despite the fact that the weakness of elliptical random number generators had been exposed in 2006 and again in 2007. Why would Bitcoin use a flawed encryption method produced by the NSA?
On October 28, 2013, an article appeared in Bitcoin Magazine claiming that Bitcoin got “lucky” because it used a Koblitz ellipse curve rather than the normal pseudo-random ellipse curve (secp256k1 rather than secp256r1).
http://bitcoinmagazine.com/7781/satoshis-genius-unexpected-ways-in-which-bitcoin-dodged-some-cryptographic-bullet/
But using a K curve rather than the R curve does not reduce the danger of the function. I know this because I have a Minor in Mathematics from Washington State University and I have spent many years studying random number generators.
In fact, the article cited several examples of how the original programmer for bitcoin, Satoshi Nakamoto, got very “lucky” in avoiding less than obvious computer programming problems in the design of bitcoin. For example, the article explains that had the maximum number of bitcoins been 210 million instead of 21 million, Bitcoin could not be represented in floating point notation making bitcoin programming much harder.
But rather than being lucky, these complex mathematical coincidences are strong evidence that Bitcoin was not designed by a single lucky person – but by many extremely smart mathematicians and computer programmers over a period of several years.
Not many high tech organizations hire both mathematicians and computer programmers. And if they did, they would not be likely to choose the NSA flawed encryption method. In other words, the strange design of Bitcoin has the fingerprints of the NSA all over it.
NSA Red Flags
The 2013 Bitcoin magazine article, which spoke so glowingly about how smart and lucky the founder of Bitcoin was, led me to dig deeper into the history of Satoshi Nakamoto and the history of Bitcoin. One of the best articles on this history was from Wired magazine in 2011. http://www.wired.com/magazine/2011/11/mf_bitcoin/
The mythical founder of Bitcoin was named Satoshi Nakamoto. In his posts, he used a fake name and a fake German email address (
While careful steps were taken to hide the actual location of the emails, a detailed analysis of his 500 posts to the Bitcoin forum indicated that Satoshi lived in the US East Coast time zone – which just happens to be the time zone where NSA headquarters are located.
In addition, Satoshi took an unusually long time - averaging two weeks - to respond to forum posts. This indicated that a group of people would prepare a response and then have it approved by senior officials before actually posting responses to the forum.
Follow the Disinterest in Money
All of these red flags aside, the biggest clue indicating that the NSA was and is behind Bitcoin comes from following the money. With the rise in the value of Bitcoins, Satoshi now has nearly $200 million dollars’ worth of bitcoins. Yet he has never cashed any bitcoins in for dollars. Just as bitcoin was gaining widespread acceptance, Satoshi suddenly stopped posting altogether and simply disappeared. What kind of person or group of persons would be willing to turn their backs on $200 million? In my book, I give other examples of the NSA throwing away billions of dollars in order to control the internet. In fact, the NSA is the only group with the money, math and computer skills needed to pull of this Bitcoin scam.
No one has ever actually met this amazingly smart, lucky and/or generous computer programmer called Satoshi. Yet he was able to do what entire teams of programmers have failed to do – establish a digital currency now worth an estimated $21 billion. Doesn’t this story seem fishy to you? To me, it reeks of the foul stench of the NSA.
Bitcoin White Paper
The NSA aka Satoshi, set up a website, bitcoin.org in August 2008 at just about the same time that the NSA started their PRISM program and the UEFI program. On the Bitcoin website, the NSA published a “white paper” under the Satoshi alias, explaining how Bitcoin works. http://bitcoin.org/bitcoin.pdf
This white paper is also very unusual. There are only a few references with the latest reference being from 2002. So why did it take Satoshi over six years to publish this white paper? In the paper, they (he) boldly state: “We have proposed a system for electronic transactions without relying on trust.” The problem with this statement is that all human transactions are based on trust relationships – except of course for the NSA where the slogan is to trust no one!
Many More NSA Red Flags
But even if this person or group of persons had revealed themselves, so that it would be possible to determine where bitcoin really came from and what the motives of the developers were, there are many other very suspicious things about bitcoin. The choice of the NSA flawed elliptical encryption method was just the first red flag.
Another major red flag is how bitcoins are initially generated. In a real digital currency, the generation of the currency would be tied to something of real value – such as gold, or silver or homes or even just a hard day’s work. This is not the case with bitcoins. They are generated by handing your Windows based computer over to some hidden third party who then uses your computer to “solve math problems.”
The first person to solve the current problem gets 50 bit coins. Because the math problems increase in difficulty over time, it takes more and more and faster and faster computers to solve the problems. This is called “bitcoin mining.” But the real mining is the data mining of the NSA.
The system they have set up to draw innocent people into this trap is diabolical in the way that it takes advantage of the human weakness for greed to encourage people to hand over their computers to the NSA in order to get a fake digital reward.
Who is behind the curtain?
The final bit of evidence is to follow the money. Who is currently using and promoting bitcoin? One group is drug dealers. Sadly, the world's largest drug dealers are the CIA and NSA. This is a primary source of their hidden income. Another group promoting bitcoin is the military (such as the US Air Force). For those not familiar with the NSA, it is actually a branch of the military and has a very close relationship with the Air Force. Why else would the Air Force get involved in promoting a digital currency based on an NSA flawed encryption method?
But ultimately, Bitcoin is not about making money. It is about controlling digital currency. This is why the NSA is willing to walk away from a quick $200 million in profits. It is clear that the NSA has the digital keys to break Bitcoin any time it wants. If and when Bitcoin finally crashes, look for the NSA to be the “man behind the curtain.”
More NSA Diabolical Plots
Bitcoin is only one of several diabolical plots being carried out by the NSA. On November 8, 2013, computer safety guru, Eugene Kaspersky, gave a talk in Australia in which he acknowledged that the Windows Flame and Stuxnet super viruses had infected Russian Windows computers controlling everything from nuclear power plants to their space station. Watch
http://www.youtube.com/watch?v=6tlUvb26DzI#t=1620
Eugene notes of the Microsoft Windows program: “Windows network for the scientists.... they come to the space station with UBS’s which are infected... These kinds of networks are not safe by design... Unfortunately, they have the very same computer as you! The attack is a virus. It can spread. If it infects an Australian power plant,. It is very possible that other nations which are not in conflict will be victims of cyber attacks on their critical infrastructure. Cyber space has no borders.” We discuss the NSA/Microsoft development of these super bugs in detail in our book. (available for free at our website Free Yourself from Microsoft and the NSA dot org).
The only good news is that governments around the world are starting to realize the need for independent branches of the internet which are not under the direct control of the NSA. This has already led to a major drop in business for US technology corporations – all of which are subject to control by the NSA. The cost to the US economy of NSA spying is already in the hundreds of billions of dollars.
Oregon Senator Ron Wyden recently remarked, "If a foreign enemy was doing this much damage to the economy, people would be in the streets with pitchforks."
Meanwhile, there have also been several toothless bills introduced into Congress to create the illusion that something will be done to reign in the NSA. None of these bills deal with the real problem which is that the NSA and Microsoft are taking over billions of computers in the world through the very dangerous UEFI – NSA startup program. The NSA is at its core the world’s most evil criminal conspiracy. The only solution to the criminal activities of Microsoft and the NSA is to shut both of them down for good.
Things are certain to get worse. The Editor of the Guardian just today stated that they have only released one percent of the Snowden documents. So read this free book and stayed tuned for more updates. https://freeyourselffrommicrosoftandthensa.org/
David Spring M. Ed. December 2, 2013

